Monitoring & hacking cell phones without their knowledge is growing rapidly in Asia countries like Australia, UK, Dubai, Sri-Lanka, Saudi Arabia, Thailand, Malaysia, Singapore, Nigeria, Kenya & South Africa after it became famous in US since 2008.
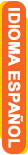
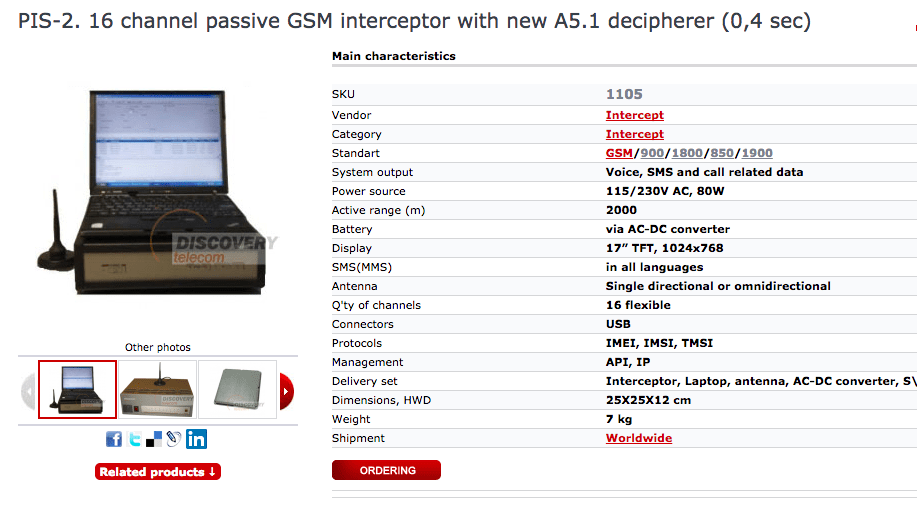
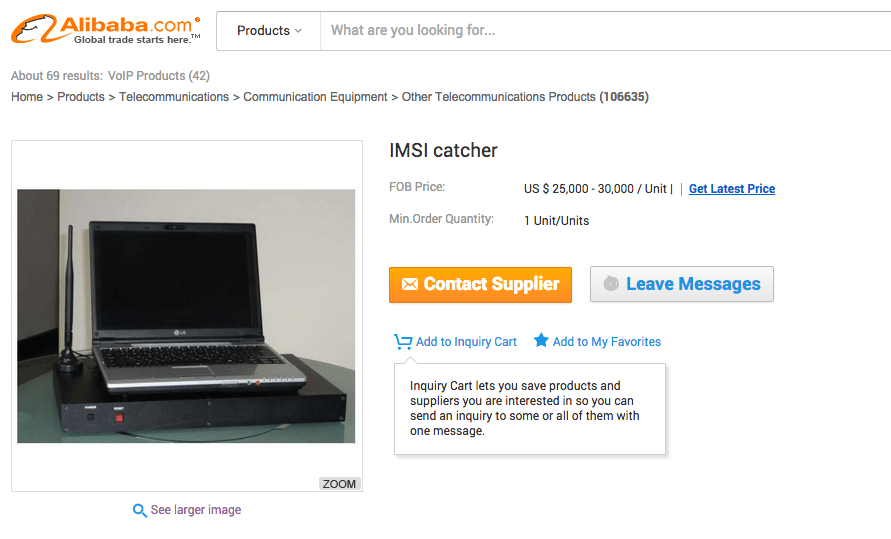
The Stingray/ GSM interceptor/IMSI catcher is equipment that can hack cell phones and gather data from hundreds of phones over targeted areas. These devices can also perform denial-of-service attacks on cellphones and intercept conversations. Though these products are not available legally, but they can be bought through black markets or through deep web.
Law enforcement and the military use these devices to track & hack cellphones. A stingray system involves an antenna, maps, and a signal device. The device mimics as a cellphone tower Base Transmitting Station (BTS) and gets the cellphones in the area to connect to it. Then it collects the International Mobile Subscriber Number (IMSI) and the Electronic Serial Number (ESM) numbers associated with the cellphone and can connect any cellphone.
There are two ways to use the devices, says Jitender Narula, a cellphone hacking training expert of the International Institute of Cyber Security.
One way is to use antenna in a given area to collect International Mobile Subscriber Numbers (IMSI) and the Electronic Serial Numbers (ESN) of the cellphones in that area and see who is in that given area. The second way is to locate a cellphone with IMEI, International Mobile Subscriber Number (IMSI) and the Electronic Serial Number (ESM) like apple Find my cell phone application but in this case the cell phone can be traced even if the cell phone is formatted, as the IMEI will remain associated with the hardware not the software. Based on the signal strength of the device you can find the exact location and hack cell phone.
Also in some cases a DOS attack can be done on a cellphone but in terms of GSM signal not in terms of Data packets. When under DOS attacks the cell phone cannot receive or make any calls.
These devices can be used with software to hack cellphone and eavesdrop on cellphone’s conversations, spoof calls and SMS. These tools are known as Over-The-Air special signal software like FISHHAWK and PORPOISE.
These devices are also knows as GSM INTERCEPTOR OR IMSI CATCHER. There are various devices like these in the market easily available. James Taylor cell phone hacking course expert, mentioned some of them are GOSSAMER, LONGSHIP, BLACKFIN, BLACKFIN II, HAWKSBILL, SPURDOG, FISHFINDER, KINGFISH, STINGRAY, STINGRAY II, GSM INTERROGATOR, CDMA INTERROGATOR, IDEN INTERROGATOR, UMTS INTERROGATOR, FISHHAWK, PORPOISE, FIREFISH, TARPON, AMBERJACK, HARPOON, MORAY, LANTERNEYE, RAYFISH, and STONECRAB. Some of these devices are easily available in market.

We will talk about a few of them below as these devices are commonly used to hack cell phones:
Gossamer like Devices

The Gossamer is a small portable device that is similar to stingray and can gather data on cellphones operating in a target area. The Gossamer device is much smaller than stingray; it can be used to perform a denial-of-service attack on cell phone users, hacking cell phones, blocking targeted people from making or receiving calls. As per analysts from the information security industry, the approximate cost of Gossamer type devices in the black market starts from 10,000 to 20,000 USD depending upon the state of device and features of the device in counties like Australia, UK, Dubai, Sri-Lanka, Saudi Arabia, Thailand, Malaysia, Singapore, Nigeria, Kenya & South Africa.
Triggerfish like devices
The Triggerfish is an eavesdropping device. With it, anybody can intercept calls, messages in real time in the targeted area and hack cellphones. It allows all the functions of stingray. Some advance Russian versions of Triggerfish can intercept calls, SMS of 10,0000 cellphones in the targeted area of city.
Kingfish like Devices

The Kingfish is a device that allows anybody to track and analyze information from cellphones over a targeted area. It is smaller than the stingray devices but it can give you the list of connections between different cell phones and hack cellphones. This device can be controlled wirelessly to monitor communications.
Harpoon like Devices
The Harpoon is an amplifier device that is used to boost the signal of a Stingray or Kingfish device, so that a big area can be monitored, and more cellphones can be tracked more safely from very far away. The cost of the harpoon like Russian amplifiers is around 15,000 USD in the black market.
3G (UMTS) networks GSM interceptor

This device automatically scans and detects parameters of all 3G networks in the range. It intercept 3G communications and data, detects all 3G cell phones and collect all their identities (IMSI, IMEI and TMSI). This device selectively blocks 3G communications of targeted cell phones. Also advance version of this device can take control of mobile devices completely to send and receive Spoof 3G related calls and data as per cellphone hacking experts.
HOW TO CREATE YOUR GSM INTERCEPTOR / STINGRAY
You can create your own GSM interceptor / stingray like device as per professor who teaches this during the cellphone hacking training.
WHAT WE NEED
BSC(base station controller) is the brain for BTS. It is the decision-making device and it decides switching among different BTS. It also does switching of calls. The interface between BSC and BTS is called GSM A-bis interface.
In our case we will use OpenBTS software to configure our software defined radio (SDR) platform which are basic radio set with can work as radio or with help of OpenBTS and Linux can be converted into an OpenBTS. We will also use Asterisk Server, which can help in call switching and is very easy to configure as BSC.
• OpenBTS is an open source software.
• Asterisk Server is also open source.
• Linux as we all know is also open source.
• Software defined radio (SDR) platform is a hardware which will cost you around 500 – 1000 USD.
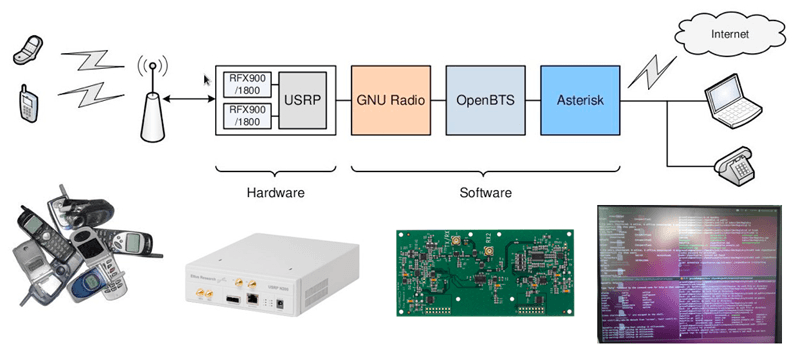
HOW IT WORKS
BTS verifies to which mobile device it’s connecting but the mobile device doesn’t verify the identity of the mobile network BTS it is connecting. Because handsets always choose the strongest signal, so if there is a new BTS with stronger signal the cellphone will connect to it always. In GSM the BTS decides to enable encryption or not, so our new OpenBTS station will be not use encryption thus we can listen to all the calls and sms. The IMSI catcher does not breaks GSM encryption; it just acts as a base station and tells the cell phone to disable GSM encryption.
In order to spoof a network and hack a cell phone we will need some information: the mobile country code, the mobile network code and the network name. All this data can easily be found on the Internet and we can program our OpenBTS with these values and configure At&t o any network. After configuring these settings in our BTS the cellphones within the range will start connecting to our OpenBTS .
We will also configure Asterisk Server, which will act as a call switching software and help us in listing to calls in real time and even recording them. You can learn to configure your own mobile network during our ethical cellphone hacking courses of iicybersecurity. This article is only for educational purposes only.
The goal of cellphone hacking and of the GSM interceptor is to help the government monitor activities of criminals. The cell phone hacking course and tools for advance cell phone surveillance for iOS & Android are only meant for government agencies. We work closely with our partners to provide cell phone hacking courses and tools in Delhi, India, Dubai and other countries. We have a partner program that recognizes the effort and investment of strategic allies, offering mobile phone surveillance solutions to achieve sustainable and mutually beneficial business. Our partners / partners program is available in Australia, UK, Dubai, Sri-Lanka, Saudi Arabia, Thailand, Malaysia, Singapore, Nigeria, Kenya & South Africa.