The detection of 4 vulnerabilities in the popular video conferencing platform Zoom has been publicly disclosed. According to the report, the successful exploitation of these flaws would allow the deployment of multiple hacking scenarios on devices with Windows, macOS, Linux, iOS and Android systems.
Below are brief descriptions of the reported flaws and their respective tracking keys and scores assigned under the Common Vulnerability Scoring System (CVSS).
CVE-2022-22787: Application software does not properly validate the hostname during a server change request, which would allow remote threat actors to deploy Man-in-The-Middle (MiTM) attacks.
The vulnerability received a CVSS score of 4.9/10, considered a medium severity risk.
CVE-2022-22786: Improper verification of the installed software version during the update process would allow remote attackers to trick the victim into installing an older Zoom version.
The flaw is considered a low severity risk and received a CVSS score of 3.7/10.
CVE-2022-22785: The Zoom client cannot properly restrict client session cookies to Zoom domains. Remote malicious hackers can obtain cookies from unsuspecting users to perform phishing attacks on the platform.
The flaw received a CVSS score of 3.1/10.
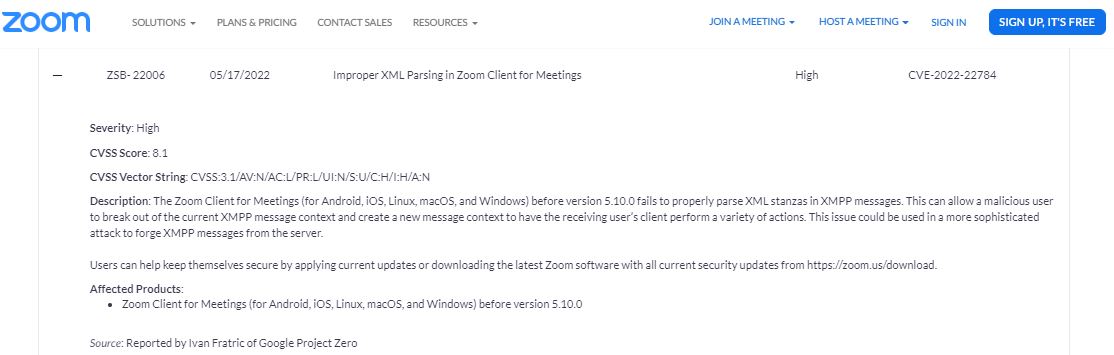
CVE-2022-22784: Incorrect input validation when processing XML data within XMPP messages would allow remote threat actors to send specially crafted messages to Zoom chat, exiting the context of the XMPP message and spoofing messages from other application users.
The vulnerability received a CVSS score of 4.7/10, considered a medium severity risk.
The report states that detected issues reside in the following versions of Zoom:
- Zoom Client for Windows: 4.0.35295.0605 – 5.5.4 13142.0301
- Zoom Client for Linux: 5.1.418436.0628 – 5.9.6 2225
- Zoom Client for macOS: 4.6.9 19273.0402 – 5.9.6 4993
- Zoom Client for Android: 4.6.11 20553.0413 – 5.9.6 4756
- Zoom Client for iOS: 4.6.10 20012.0407 – 5.9.6 2729
While unauthenticated, remote threat actors can exploit flaws, no active exploitation attempts have been detected. Still, Zoom recommends users of affected deployments update as soon as possible.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.








