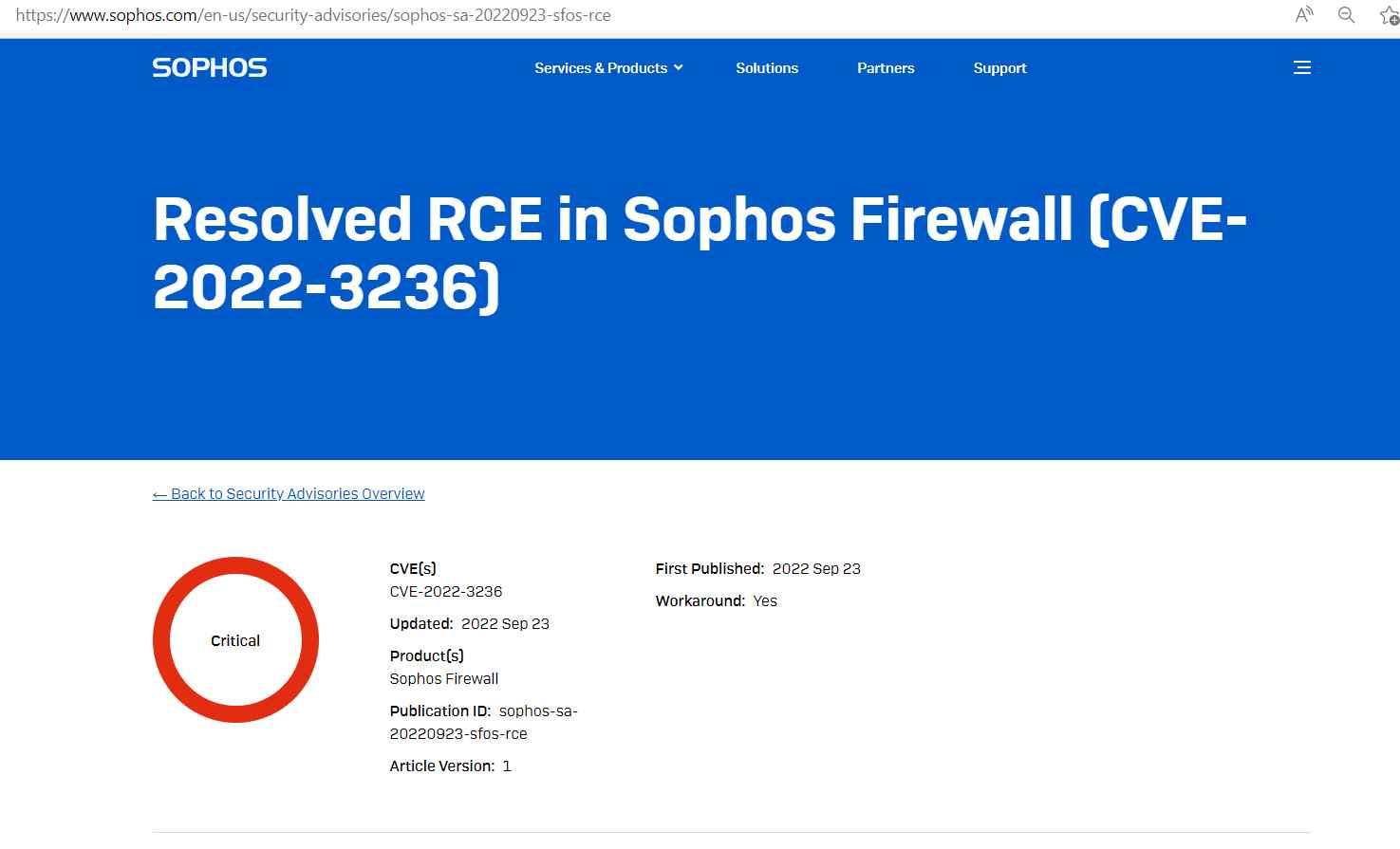
A security alert concerning CVE-2022-3236, a code injection flaw that impacts the Sophos Firewall’s User Portal and Webadmin and might be used to remotely execute malicious code, was released by the British cybersecurity company Sophos.
Sophos has seen that a small number of targeted companies, mostly in the South Asia region, are being attacked using this flaw. Each of these businesses has received a direct message from us. Sophos will give further information as they continue the investigation.
Users of Sophos Firewall who have the “Allow automatic installation of hotfixes” functionality activated don’t need to take any action (see Remediation section below).
Workaround
By making sure that their User Portal and Webadmin are not accessible to WAN, companies can safeguard themselves from possible threats.
Implement device access best business practices to disable WAN access to the User Portal and WebAdmin, and instead utilize VPN and/or Sophos Central (recommended) for remote access and control.
Remediation
Make sure you are using a version that is supported.
On September 21, 2022, the following versions received hotfixes:
MR1, MR1-1, and v19.0 GA
MR1, MR1-1, MR2, MR3, and MR4 for version 18.5 GA
On September 23, 2022, the following versions received hotfixes:
Version 18.0, MR3, MR4, MR5, and MR6
MR12, MR13, MR14, MR15, MR16, and MR17 of version 17.5
v17.0 MR10
v18.5 MR5 (18.5.5), v19.0 MR2 (19.0.2), and v19.5 GA all have the fix.
To acquire the most recent defenses, users of earlier Sophos Firewall versions must update, and this workaround








