In its latest security alert, the team behind Drupal reported finding a set of severe vulnerabilities in a third-party library. Successful exploitation of the flaws would reportedly allow threat actors to remotely hijack any website using the technology of this content management system (CMS).
The flaws were tracked as CVE-2022-31042 and CVE-2022-31043 and reside in Guzzle, a third-party library that Drupal uses for managing HTTP requests and responding to external services: “These issues do not affect the Drupal core, but may affect some contributed projects or custom code on Drupal sites.”
Because Guzzle has already released some details about the flaws, Drupal considered it pertinent to publish a new report on the matter. In addition, there are likely to be other flaws in custom modules that use Guzzle for outbound requests.
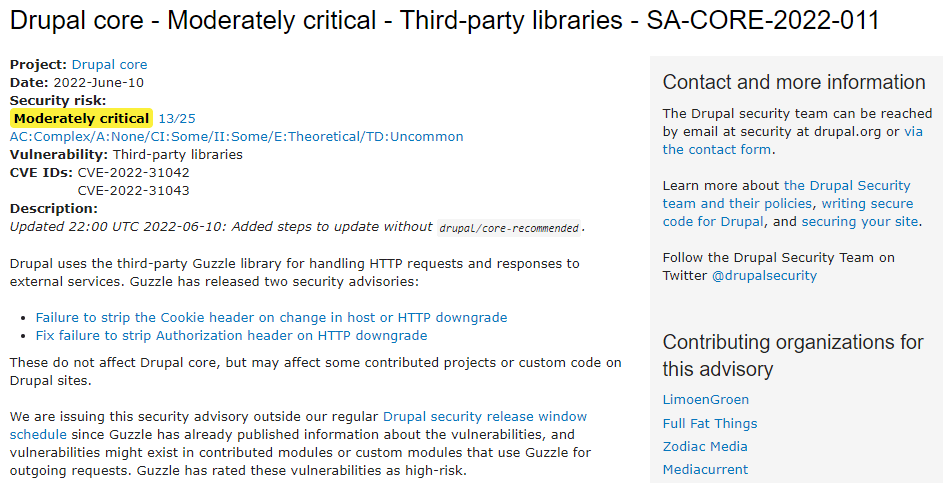
Guzzle assigned high-risk scores to these flaws, while Drupal warns that bugs can affect some contributed projects or custom code on Drupal sites: “Exploiting these issues would allow remote attackers to take control of an affected website.”
Guzzle issued separate notices documenting errors such as a failure during cookie header deletion in host change or HTTP degradation and a failure to remove the authorization header in HTTP degradation. The security team recommends its users to install the latest versions (Drupal 9.2 to Drupal 9.4). It is important to note that all versions of Drupal 9 prior to 9.2.x are at the end of their lifecycle and will not receive updates.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.








