A cybersecurity specialist at SEC Consult reported the finding of five different vulnerabilities residing in Pepperl+Fuchs Comtrol IO-Link industrial control devices, including attack variants such as cross-site request forgery (CSRF), cross-site scripting (XSS) attacks, injection of arbitrary commands, and denial of service (DoS).
A successful attack is possible by exploiting unpatched vulnerabilities in outdated versions of these products, as well as some flaws in third-party components such as PHP, OpenSSL, BussyBox, and the Linux kernel. The report prepared by cybersecurity experts contains the proof-of-concept (PoC) code for each one of the detected flaws.
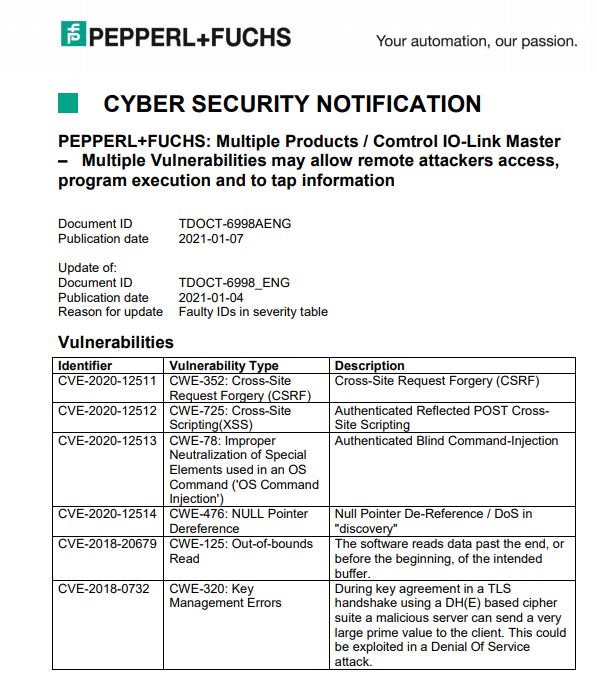
Pepperl+Fuchs issued a cybersecurity alert mentioning that these vulnerabilities would allow threat actors to gain access to affected devices, running any program, and extracting all kinds of sensitive information.
According to Johannes Greil, senior consultant at SEC Consult, if a malicious hacker manages to gain access to one of the vulnerable Comtrol devices (via an XSS attack or by brute force), he could gain the ability to execute commands on the target device with root privileges, which would even allow the installation of persistent backdoors.
IO-Link is an industrial communications protocol used for the operation of sensors and digital actuators. The manufacturer states that the IO-Link Master product family “combines the benefits of the IO-Link standard with EtherNet/IP and Modbus TCP protocols”. The IO-Link Master effectively protects PLC programmers from the complexities of IO-Link by handling those complexities by itself.
The company’s security teams corrected the vulnerabilities detected up to a few months after receiving the SEC Consult report. Pepperl+Fuchs acknowledges that at least a dozen of its products would be affected by these failures, so it strongly asks customers to upgrade the U-Boot boot loader to mitigate the risk of exploitation.








