Cisco’s cybersecurity teams announced the release of a patch set to address several critical vulnerabilities, including security flaws in Webex Player, SD-WAN and ASR 500 Series software, used in all sorts of environments. The three most severe flaws received scores of 7.8/10 according to the Common Vulnerability Scoring System (CVSS) and reside in Webex Player for Windows and macOS systems, in addition to affecting Webex Network Recording Player for the aforementioned operating systems.
The first of the flaws found was tracked as CVE-2021-1526 and described as a memory corruption problem whose successful exploitation would allow code execution on the target system. The flaw can be exploited via Webex Recording Format (WRF) files and resides in Cisco Webex Player versions prior to v41.5.
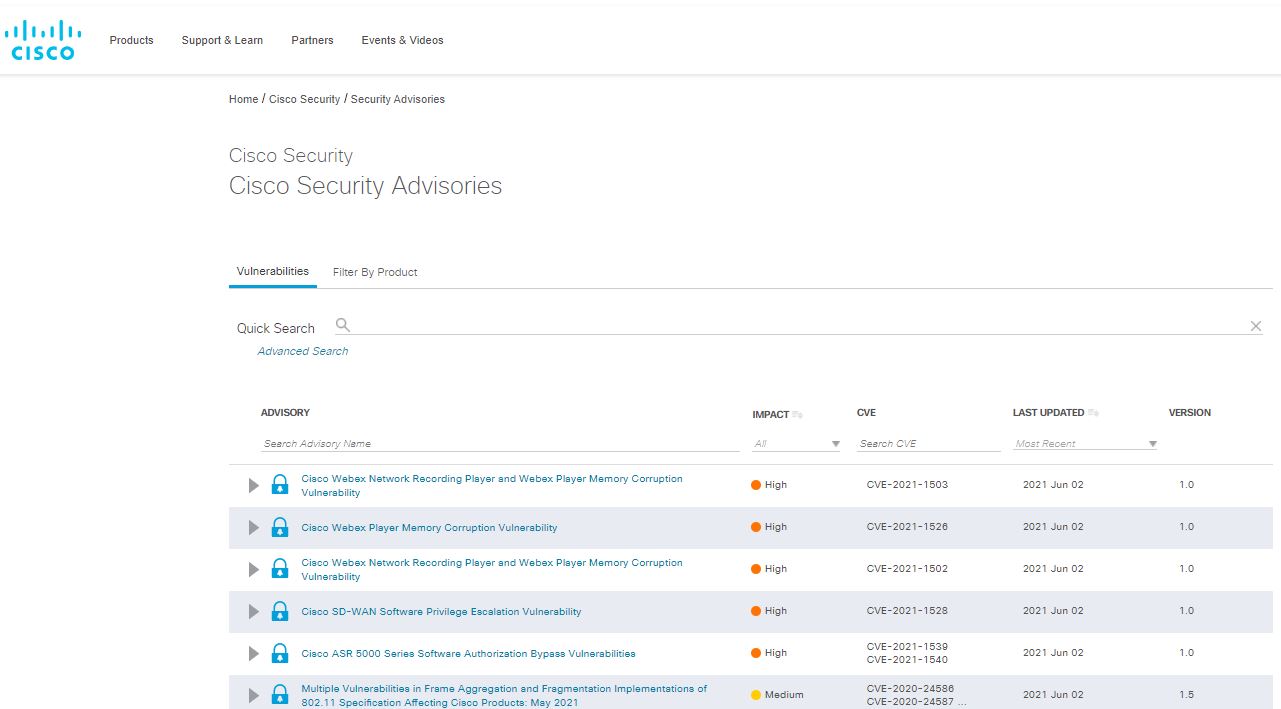
The following two flaws (CVE-2021-1502 & CVE-2021-1503) were also described as memory corruption errors in Webex Network Recording Player and Webex Player for macOS and Windows. The two vulnerabilities could be exploited to lead to arbitrary code execution scenarios on the affected systems; to avoid this scenario, users should upgrade to v14.4 and later versions.
This has been a busy week for Cisco cybersecurity teams. A couple of days ago the company also released security patches to address CVE-2021-1528, a critical flaw (CVSS of 7.8/10) in SD-WAN. This flaw could be exploited by malicious actors in order to gain elevated privileges on the target system. The flaw resides in SD-WAN versions 20.4 and 20.5 and should be corrected by upgrading to v20.4.2 or 20.5.1.
The company also released patches for a pair of vulnerabilities in the ASR 5000 series (StarOS) software that could be exploited to bypass security controls and execute CLI commands on a vulnerable system. A full report of these flaws can be found on Cisco’s official platforms.
As usual, Cisco invites users of vulnerable deployments to upgrade to the corrected versions as soon as possible. The company concluded its message by assuring that so far no active exploitation attempts have been detected, although this is no reason not to update the affected systems.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.








