Information security specialists report the detection of two vulnerabilities in Vim, the improved version of the Vi text editor, present in all UNIX systems and developed by Bram Moolenar in 1991. According to the report, the successful exploitation of these flaws would allow a severe compromise of the affected systems.
Below are brief descriptions of the reported vulnerabilities, in addition to their respective tracking keys and scores assigned according to the Common Vulnerability Scoring System (CVSS).
CVE-2022-1619: A boundary error when processing data in the cmdline_erase_chars() function in ex_getln.c would allow remote hackers to trigger a heap-based buffer overflow, leading to arbitrary code execution on the affected system.
This is a high severity flaw and received a CVSS score of 7.7/10.
CVE-2022-1620: A NULL pointer dereference error within the vim_regexec_string() function in regexp.c would allow remote hackers to trigger a denial of service (DoS) condition on the application.
The flaw received a CVSS score of 3.8/10 and is considered a low severity error.
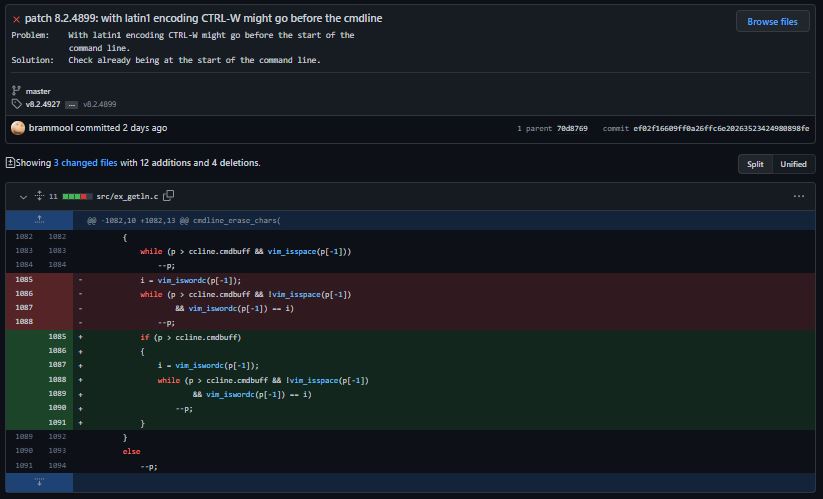
According to the report, the flaws reside in all versions of Vim between Vim: 8.2.4800 and 8.2.4898.
While these vulnerabilities can be exploited by unauthenticated remote threat actors, so far no active exploitation attempts or the existence of a malware variant related to the attack have been detected. Still, users of affected deployments are encouraged to update as soon as possible to mitigate the risk of exploitation.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.








