Cloud security course specialists report the finding of two critical vulnerabilities in Apache Struts, the MVC pattern web application development support tool under the Java EE platform. According to the report, exploiting these flaws would allow malicious code execution and bypass security controls in affected deployments.

Below is a brief description of the reported flaws, in addition to their respective identification keys and scores according to the Common Vulnerability Scoring System (CVSS).
CVE-2019-0230: By forcing Apache Struts frameworks it is possible to double evaluate the values of attributes assigned to certain tag attributes (such as id) so it is possible to pass a value that will be evaluated again when the attributes of a tag are displayed, which threat actors could leverage to execute arbitrary code on the target system.
According to cloud security course experts, it is possible to use a specially designed request to complete the attack, although the problem is only triggered when the OGNL evaluation is forced within a Struts tag attribute, when the expression to be evaluated refers to an non valid and unprocessed entry, as shown below:
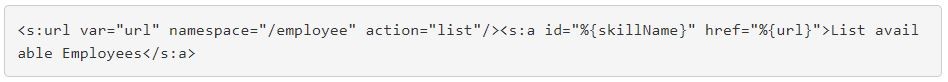
If a threat actor can modify the skillName attribute in a request so that a raw OGNL expression is passed to the skillName property without further validation, the supplied OGNL expression contained in the skillName attribute is evaluated when the tag is rendered as a result of the request.
This is a high severity flaw that received a score of 8.5/10.
In their report, cloud security course specialists mention: “We’ve identified several proof-of-concept (PoC) examples on GitHub for CVE-2019-0230. However, it is important to note that because each Struts application is unique, the actual payload required to exploit it will differ from application to application. In addition, the application should be developed in such a way as to allow an attacker to provide unvalidated information in an attribute used within an OGNL expression”.
CVE-2019-0233: Values accessible to the java.io.File and java.nio.File stack, as well as other classes in these standard library packages are not adequately protected by the framework, so threat actors might deploy a denial of service (DoS) condition.
When a file is uploaded to an action that exposes the file with a getter, a malicious hacker may manipulate the request; as a result, subsequent actions on the file will show an error. It is also possible to configure the temporary directory of the Servlet container to read-only, so subsequent load actions will fail. The flaw received a score of 5.7/10, so it is considered a risk of average severity.
Apache Struts affected by these flaws are: 2.0.0, 2.0.1, 2.0.2, 2.0.3, 2.0.4, 2.0.5, 2.0.6, 2.0.7, 2.0.8, 2.0.9, 2.0.10, 2.0.11, 2.0.11.1, 2.0.11.2, 2.0.12, 2.0.13, 2.0.14, 2.1.0, 2.1.1, 2.1.2, 2.1.3, 2.1.4, 2.1.5, 2.1.6, 2.1.7, 2.1.8, 2.1.8.1, 2.2.0, 2.2.1, 2.2.1.1, 2.2.2, 2.2.3, 2.2.3.1, 2.3.1, 2.3.1.1, 2.3.1.2, 2.3.2, 2.3.3, 2.3.4, 2.3.4.1, 2.3.5, 2.3.6, 2.3.7, 2.3.8, 2.3.9, 2.3.10, 2.3.11, 2.3.12, 2.3.13, 2.3.14, 2.3.14.1 , 2.3.14.2, 2.3.14.3, 2.3.15, 2.3.15.1, 2.3.15.2, 2.3.15.3, 2.3.16, 2.3.16.1, 2.3.16.2, 2.3.16.3, 2.3.17, 2.3.19, 2.3.20, 2.3.20.1, 2.3.20.2, 2.3.20.3, 2.3.21, 2.3.22, 2.3.23, 2.3.24, 2.3.24.1, 2.3.24.2, 2.3.24.3, 2.3.25, 2.3.26, 2.3.27, 2.3.28, 2.3.28.1, 2.3.29, 2.3.30, 2.3.31, 2.3.32, 2.3.33, 2.3.34, 2.3.35, 2.3.36, 2.5, 2.5.1, 2.5.2, 2.5.3, 2.5.4, 2.5.5, 2.5.6, 2.5.7, 2.5.8, 2.5.9, 2.5.10, 2.5.10.1, 2.5.12, 2.5.13, 2.5.14, 2.5.14.1, 2.5.16, 2.5.17, 2.5.18, 2.5.20.
While these vulnerabilities can be exploited remotely by unauthenticated threat actors, specialists have not detected active exploit attempts, although as mentioned above, an exploit is available on GitHub. Apache Struts managers have already released the corresponding updates, so affected deployment administrators should only verify their correct installation.








